A recent Google ads campaign, active for an extended period, likely delivered Cobalt Strike deployments to unsuspecting victims, according to researchers.
Malwarebytes cybersecurity experts uncovered the campaign, which exploited Google Ads targeted at users seeking Notepad++, a widely-used text editing tool.
When users queried Notepad++ or related terms, the initial search results included ads, some of which directed them to malicious websites.
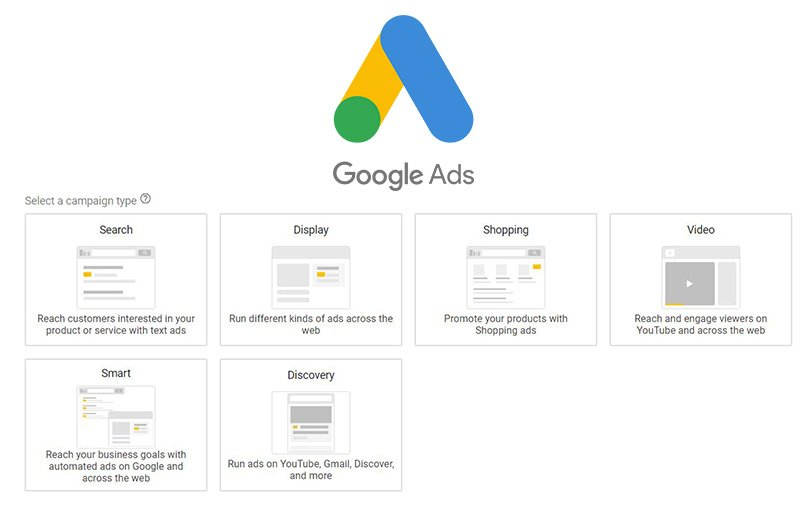
Google Ads Campaign Tactics and Malware Warnings
Cobalt Strike is a familiar tactic, repeatedly observed. Notably, on the search engine results page, site titles appear in larger fonts, making users prone to overlooking verification and clicking suggested results.
Moreover, Google is widely perceived as a trusted platform where users rarely scrutinize the websites displayed, particularly on the first page.
Once a user clicks the link, the site conducts preliminary authenticity checks, ensuring the visitor is genuine and not a bot or VPN user. Subsequently, it presents a site closely mirroring the legitimate Notepad++ page. For those identified as bots or unsuitable visitors, a decoy site redirects them, while repeat visitors encounter a 404 error.
During the analysis, Malwarebytes couldn’t inspect the actual payload. However, researchers speculate the attackers likely deployed Cobalt Strike, often preceding ransomware deployment, as reported by BleepingComputer.
Abusing ad networks is not a novel concept. Cybersecurity experts emphasize user vigilance when online activities are concerned, urging double-checking the legitimacy of software sources. Illegitimate software, often distributed through email links or social media messages, is almost always malicious.

